SOHO NETWORK
Requirement, Planning and Implementation
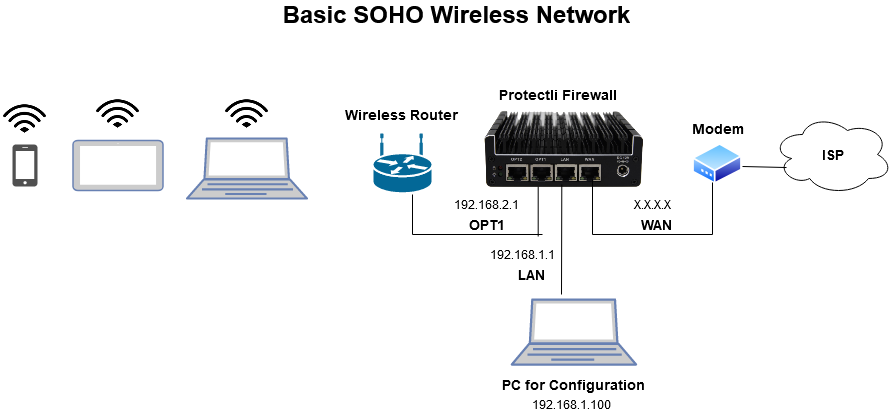
SOHO network or also termed as single or small office/home office network is mainly referred to a business category involving a small number of workers usually from 1 to 10. It is a type of local area or LAN network connection meant to be used in small businesses.
Like many other LANS, SOHO network may also be a mixture of networks of wireless or wired computers. The SOHO router is more or less the conventional broadband router designed to be operated in such organizations.
A SOHO network may also support a bit larger group of peoples and is generally a privately owned or owned by self employed individuals for a smaller business organization.
SOHO, nowadays, is becoming more and more popular in different sectors including networking circles. As there is increase in the number of smaller business units, the call for SOHO networks is also in demand and is on the rise day by day.
The features and benefits provided by SOHO such as easy to use and setup network etc. makes them an ideal choice for the same. Virtual office is another synonym sometimes used for a SOHO network. SOHO networking is mainly used for the purpose of connecting several computing devices on a single network to share the information effectively with the connected multiple users in the organization.